The cybersecurity landscape is shifting beneath our feet. As threat actors begin to leverage autonomous tools, security professionals are finding that traditional, manual penetration testing often struggles to keep pace with the sheer scale of modern attack surfaces. Enter BlacksmithAI, a groundbreaking open-source AI-powered penetration testing framework designed to mirror the sophisticated coordination of a human Red Team.
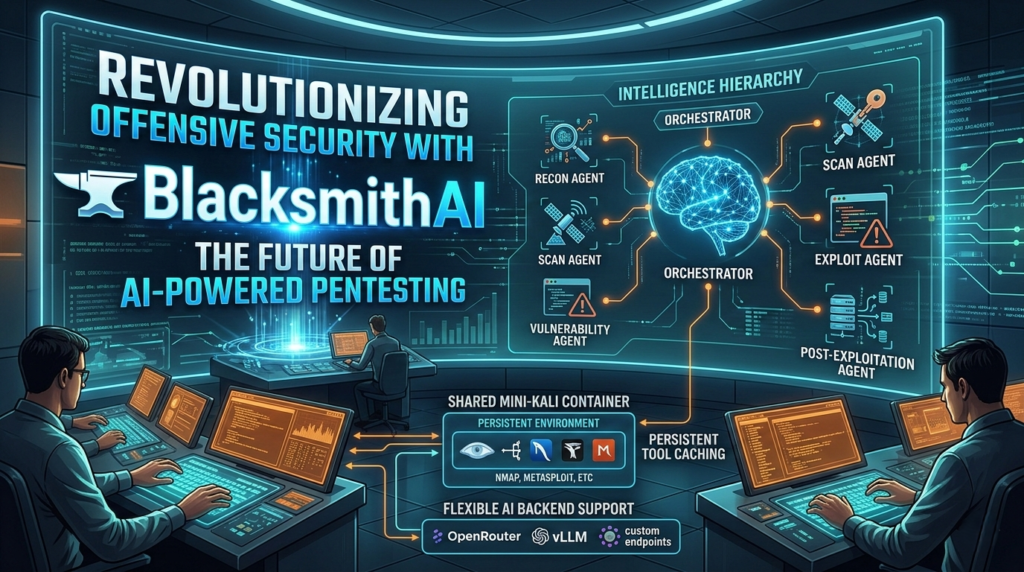
Unlike first-generation AI security tools that rely on a single, overwhelmed “super agent,” BlacksmithAI introduces a hierarchical, multi-agent architecture. This approach doesn’t just automate tasks; it orchestrates a specialized workforce of digital experts to identify, analyze, and validate vulnerabilities with unprecedented efficiency.
What is BlacksmithAI?
At its core, BlacksmithAI is an offensive security framework that utilizes Large Language Models (LLMs) to power a team of autonomous agents. Each agent is purpose-built for a specific phase of the penetration testing lifecycle. By distributing intelligence across these specialized roles, the framework achieves a level of depth and reliability that single-agent systems simply cannot match.
The system operates within a “mini-Kali” environment—a shared container pre-loaded with industry-standard tools. This ensures that the BlacksmithAI agents have immediate access to the utilities they need without the overhead of spinning up new environments for every individual sub-task.
The Multi-Agent Architecture: How It Works
The true power of this BlacksmithAI framework lies in its organizational structure. It mimics a professional security firm where a Lead Auditor (the Orchestrator) manages several specialists.
1. The Orchestrator (The Mastermind)
The Orchestrator is the brain of the operation. It interacts with the user, defines the scope, and breaks down complex security objectives into manageable sub-goals. It decides which specialist agent is best suited for the task at hand and compiles their findings into a cohesive final report.
2. Specialized Sub-Agents
Each sub-agent in BlacksmithAI is equipped with its own domain expertise and toolset:
- Recon Agent: Focuses on attack surface mapping and information gathering using tools like
WhoisandDig. - Scan & Enumeration Agent: Handles service discovery and identifies open ports or hidden directories.
- Vulnerability Analysis Agent: Evaluates the gathered data to pinpoint potential weaknesses and exposures.
- Exploit Agent: Executes safe, proof-of-concept activities to confirm if a vulnerability is truly “patch-worthy.”
- Post-Exploitation Agent: Examines the potential impact and identifies opportunities for lateral movement within a network.
Key Features of the BlacksmithAI Framework
The developer, Yohannes Gebrekirstos, designed BlacksmithAI to be lightweight, extensible, and high-performance. Here are the standout features that make it a formidable tool for modern security teams:
| Feature | Description |
| Hierarchical Intelligence | Tasks are delegated from a central orchestrator to specialized agents, preventing “reasoning fatigue.” |
| Shared Container Environment | Uses a persistent, pre-configured Docker environment (mini-Kali) to save memory and time. |
| LLM Agnostic | Supports various backends including OpenRouter, vLLM, and custom endpoints. |
| High Performance | Built with FastAPI and the uv package manager for rapid execution and tool caching. |
| Extensible Design | Easily add new agents, skills, or tools via Model Context Protocols (MCPs). |
Why the Industry is Moving Toward AI-Powered Pentesting
Traditional automated scanners often produce “noise”—hundreds of false positives that require hours of manual triage. BlacksmithAI aims to solve this by applying LLM-based reasoning to the results. Instead of just flagging a version number, the agents can cross-reference findings, attempt low-level validation, and provide a reasoned argument for why a specific finding matters.
Furthermore, the BlacksmithAI framework is highly accessible. Whether you are running it on Linux, macOS, or Windows (via WSL2), the deployment process is streamlined through Python 3.12 and Node.js components.
Actionable Insights for Security Teams
If you are looking to integrate an BlacksmithAI workflow into your current security stack, consider the following strategies:
Continuous Monitoring, Not Periodic Audits
Don’t wait for your annual pentest. Use the BlacksmithAI framework to run weekly or even nightly “smoke tests” against your external infrastructure. This allows you to catch regressions or misconfigured assets in near real-time.
Bridging the Skills Gap
The cybersecurity industry faces a chronic talent shortage. While BlacksmithAI does not replace a senior pentester, it acts as a force multiplier. It allows junior analysts to manage complex workflows and ensures that the “boring” parts of recon and scanning are handled autonomously, freeing up humans for deep-dive creative exploitation.
Safe Validation of Vulnerabilities
One of the most valuable aspects of BlacksmithAI is its ability to perform proof-of-concept (PoC) activity. By configuring the Exploit Agent correctly, you can move beyond theoretical vulnerabilities and see exactly how a flaw could be leveraged, providing better data for your remediation teams.
The Future Roadmap: Interactive Tools and Web Testing
The current iteration of BlacksmithAI is already powerful, but the future looks even more promising. Upcoming updates are expected to include:
- Interactive Tool Support: Integration with heavyweights like Metasploit and BeEF.
- Browser-Based Testing: Moving beyond CLI tools to interact with web elements, filling forms, and clicking buttons via Playwright.
- Skill Acquisition: Allowing agents to “learn” best practices by reading tool documentation and combining multiple utilities in novel ways.
By utilizing BlacksmithAI, security researchers can scale their efforts without the friction typically associated with large-scale manual testing.
Getting Started with BlacksmithAI
To deploy BlacksmithAI in your environment, you will need to ensure your system meets the basic requirements:
- Docker: For the containerized “mini-Kali” environment.
- Python 3.12+: The core language powering the agent logic.
- uv Package Manager: For fast and reliable dependency management.
- API Access: A key for an LLM provider (like OpenRouter) or a locally hosted model via vLLM.
Once these are in place, you can clone the repository from GitHub and begin your first automated security assessment. Because BlacksmithAI is open-source, the community is encouraged to contribute new “skills” and agents, ensuring the tool evolves as fast as the threats it seeks to stop.
Final Thoughts on BlacksmithAI
The release of BlacksmithAI marks a significant milestone in the democratization of advanced offensive security tools. By combining the precision of traditional security utilities with the reasoning capabilities of modern AI, it provides a glimpse into a future where security is proactive, autonomous, and scalable.
Whether you are a Red Team lead looking to optimize your workflow or a developer wanting to secure your application, the BlacksmithAI framework offers a sophisticated, multi-agent solution that is built for the challenges of 2026 and beyond.