The rise of autonomous AI agents has often been described as a “Wild West” for enterprise IT departments. While open-source frameworks like OpenClaw have seen unprecedented adoption—surpassing even Linux in GitHub star velocity—they have historically lacked the safety rails required for corporate production. Large organizations cannot risk an agent accidentally deleting an inbox, leaking sensitive PII to a cloud model, or making unauthorized network connections.
Enter NVIDIA NemoClaw. Announced at GTC 2026, NemoClaw is NVIDIA’s answer to the “security dumpster fire” often associated with ungoverned agents. By wrapping the power of OpenClaw in a sophisticated security and privacy stack, NVIDIA is effectively turning a personal AI experiment into enterprise-grade infrastructure.
What is NVIDIA NemoClaw?
At its core, NVIDIA NemoClaw is an open-source stack that integrates the OpenClaw agent platform with the NVIDIA Agent Toolkit. It provides a single-command installation that adds essential privacy and security controls, making self-evolving agents safe for both cloud and on-premises deployments.
Think of OpenClaw as the powerful engine and NemoClaw as the armored vehicle built around it. It ensures that while the agent is “productive,” it remains within a defined “sandbox” where every action is governed by declarative policy.
The Three Pillars of NVIDIA NemoClaw Architecture
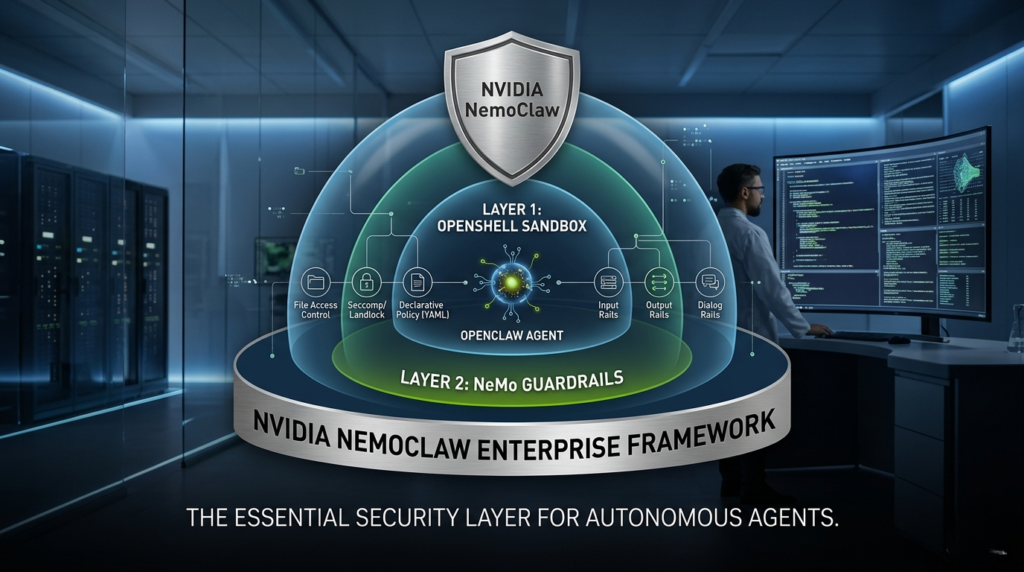
To understand how NVIDIA NemoClaw secures the agentic workflow, we must look at its three-layer defense-in-depth strategy.
1. OpenShell: The Security Sandbox
OpenShell is the brand-new open-source runtime that serves as the execution layer for agents. Instead of running directly on the host OS with broad permissions, the agent lives inside a sandbox.
- File Access Control: Agents can only access files explicitly relevant to their current task.
- Landlock & Seccomp: Utilizes Linux security modules to restrict system calls.
- Declarative Policy: IT teams can use YAML manifests to define exactly what the agent is allowed to do.
2. NeMo Guardrails: The Conversational Layer
Building on NVIDIA’s established NeMo Guardrails toolkit, NVIDIA NemoClaw applies programmable “rails” to the interaction itself.
- Input Rails: Reject or mask sensitive user prompts before they reach the model.
- Output Rails: Screen the agent’s responses to prevent the disclosure of confidential data or the generation of harmful content.
- Dialog Rails: Force the agent to follow specific conversational flows, ensuring it stays on-topic.
3. The Privacy Router: Local vs. Cloud Inference
One of the biggest hurdles for enterprise AI is data residency. NVIDIA NemoClaw solves this through a Privacy Router that manages how data flows to Large Language Models (LLMs).
- Local Execution: By default, agents can run on local NVIDIA RTX-powered PCs or DGX servers using Nemotron models.
- Secure Cloud Routing: If a frontier model (like GPT-4 or Claude) is needed, the Privacy Router scrubs the request of sensitive data before it leaves the local environment.
OpenClaw vs. NVIDIA NemoClaw: A Comparison for Enterprises
For developers, OpenClaw is a dream because of its low friction. For CSOs, NVIDIA NemoClaw is a necessity for compliance and risk management.
| Feature | OpenClaw (Community) | NVIDIA NemoClaw (Enterprise) |
| Primary Goal | Accessibility and Speed | Security, Privacy, and Scale |
| Security Model | Permissive (User-managed) | Mandatory Sandbox (OpenShell) |
| Governance | Manual API configurations | Declarative YAML Policies |
| Identity | Basic API Keys | Native SSO (Okta, Entra ID) |
| Auditability | Standard logs | Immutable Audit Ledgers |
Why Every Company Needs a NemoClaw Strategy
NVIDIA CEO Jensen Huang famously stated that “OpenClaw is the operating system for personal AI.” If that is the case, then NVIDIA NemoClaw is the enterprise edition that makes it viable for business.
Without a stack like NVIDIA NemoClaw, companies are faced with a difficult choice: block agentic AI and lose a competitive edge, or allow it and risk catastrophic data breaches. By providing a “single command” path to security, NVIDIA is removing the friction that has kept enterprises on the sidelines.
Actionable Insights for Implementation
If you are looking to deploy NVIDIA NemoClaw within your organization, consider these three steps to ensure a smooth transition from prototype to production:
- Define Least Privilege Early: Use the YAML policy manifests in OpenShell to restrict your agents to specific directories and network endpoints from day one.
- Leverage Local Nemotron Models: For tasks involving highly sensitive internal data, configure NVIDIA NemoClaw to use local Nemotron models on RTX workstations to keep data entirely offline.
- Audit the “Claw”: Regularly review the immutable audit ledgers provided by the platform to identify if agents are attempting to overstep their bounds or if prompt injection attacks are being successfully neutralized.
Conclusion: The New Renaissance in Software
The arrival of NVIDIA NemoClaw marks the end of the experimental phase of AI agents. We are moving into an era where “always-on” assistants will handle procurement, customer support, and software development autonomously. With the right guardrails in place, the “Agent Renaissance” isn’t just a possibility—it’s a secure reality.